Fortifying Digital Data Centers: Essential Physical Security Systems for the Modern Era
Part 1: Protection from the First Line of Defense
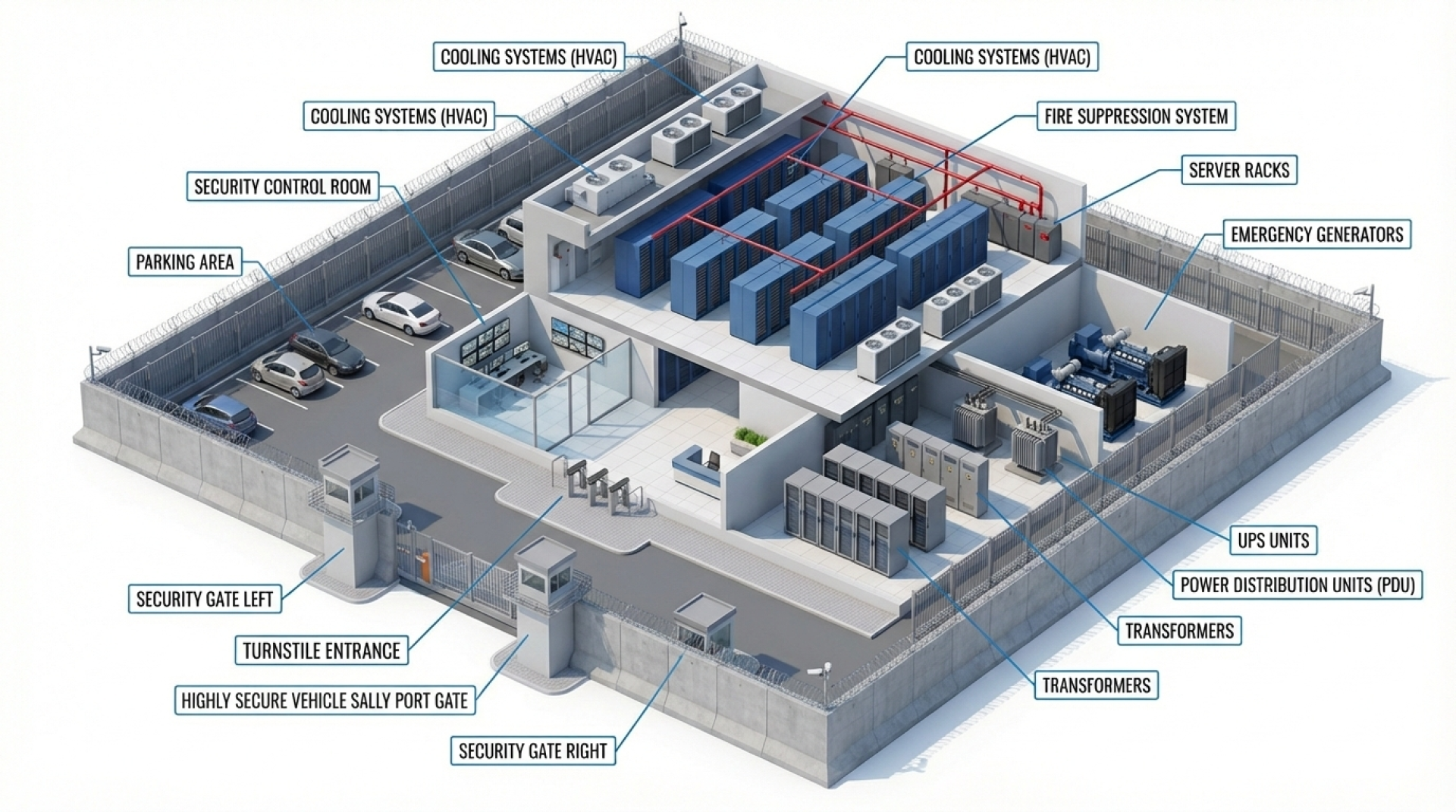
High-Security Fencing and Barriers Anti-climb fencing systems can be integrated with electric security features to enhance protection levels. This includes dual-layer interlocking fences to screen and verify individuals before they enter the main facility. Combined with high-precision CCTV and License Plate Recognition (LPR) systems, these measures provide a comprehensive record of all entry and exit data. AES Group provides expert design and installation services for fencing and barrier systems tailored to the specific needs of each organization.
Hostile Vehicle Mitigation (HVM) Vehicle ramming attacks against perimeter fences or gates are a real and serious threat. Installing bollards, crash barriers, and gates that meet international standards—such as PAS68 and IWA14-1—effectively prevents breaches by heavy vehicles. These systems can be integrated with a Command Centre for centralized management.
Perimeter Intrusion Detection Systems (PIDS) Fencing is only effective if it can detect intrusions in real-time. PIDS technologies—such as fence-mounted vibration sensors, microwave beams, ground radar, and infrared sensors—can immediately detect climbing, cutting, or trespassing. Alerts are sent instantly to the control room, allowing security personnel to respond rapidly.
Part 2: Interior Access Control
Once the outer perimeter is cleared, controlling access within the building is crucial to ensuring only authorized personnel can reach sensitive areas.
Access Control Systems Automated turnstiles can be linked with CCTV systems and central management platforms (Command Centres) to record detailed entry/exit logs for retrospective auditing and real-time monitoring.
Multi-Factor Authentication (MFA) Relying on access cards alone may not be sufficient for high-security environments. Combining cards with fingerprint scanning, facial recognition, or touchless biometric technologies—such as MorphoWave—significantly enhances security and eliminates the risk of identity spoofing.
Part 3: Maximum Protection for Critical Internal Areas
Critical zones within a data center such as server rooms, cooling infrastructure, and data storage areas—require the highest level of restricted access.
Smart Rack Locking Systems Intelligent server rack locks that support Smart Cards, PINs, and biometrics allow for individualized access rights (e.g., for specific technicians or engineers). Every instance of access is recorded in detail 24/7 to maintain a strict audit trail.
Surveillance and Command Centres — A dedicated Security Command Centre consolidates data from cameras, sensors, and other security subsystems into a single unified platform. This enables staff to monitor, analyze, and respond to incidents around the clock.
Intelligent CCTV Systems High-resolution cameras with low-light capability and Wide Dynamic Range (WDR), powered by AI analytics—such as facial recognition, people counting, and behavioral analysis—elevate CCTV from a passive recording tool to a proactive surveillance system.
AES Group has over 30 years of experience in designing and installing end-to-end security solutions, from external perimeters to internal command centres. We serve data centers, industrial facilities, state enterprises, and government agencies nationwide, adhering to international standards and specialized technical expertise.
We are ready to provide consultation, design, and installation for security solutions tailored to your organization, protecting your assets, data, and business continuity with world-class standards.


